The ASP.NET Precompiler action allows you to compile ASP.NET applications before deployment. Precompiling has two main advantages:
Compiler Options
|
|
|
There are three ways to specify the path to your ASP.NET Application:
The application will be located by using the IIS metabase and the default website. The physical (local) folder will be determined via the IIS metabase.
The application will be compiled from the specified physical (local) directory, but as if it was installed at the IIS virtual directory given by the path. This is useful if you want to compile your ASP.NET application from one (offline) directory, but deploy the assemblies in another directory.
The application will be located by using a full IIS metabase path. The physical (local) folder will be determined via the IIS metabase.
The directory that the precompile will be based in. If not set then its the currently working directory of the build.
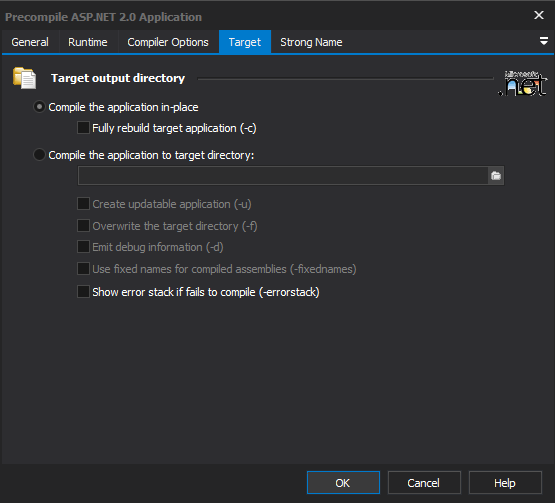
The application will compile to the same directory as the source.
All sources will be rebuilt, not just those which have changed.
The application will compile to the specified target directory. Compiling to a target directory automatically implies "fully rebuild target application."
The compiled application will be updatable.
If the target directory already exists, its contents will be overwritten.
The compiler will emit debug information to the log during the compile process.
The compiled assemblies will be given fixed names. If this option is not set, the names will be automatically generated.
Specify if a stack trace is required in the action output when a failure occurs.
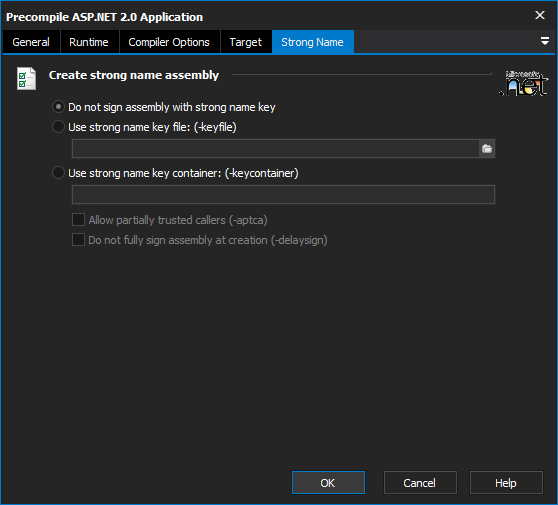
Choose not to sign the assemblies with a strong name. This means that weak naming is required to reference any assemblies created.
The filename which has the public/private key pair to be used in generating the strong name.
The name of the container which has the public/private key pair to be used in generating the strong name.
This allows the produced code to be accessed by partially trusted callers.
Specifies that the assembly should only be signed with the public key token rather than the public/private key pair. The produced code can be run before signing is completed. Take great care that no malicious users can access before signing has been completed.